Cryptography
Cryptography is a technique that converts plain text into an encrypted text. It is challenging for a third party to change the data while using cryptography.
Cryptography ensures
- Security of the network
- Transparency in transactions
- Privacy of the individual users
Why cryptography in Blockchain?
The term “cryptography” refers to much more than simply the encryption and decoding process.
Cryptography is useful for
- Creating a digital signature: A mathematical formula that verifies the legitimacy of an electronic communication
- Dividing a complex message into simpler ones or doing even more sophisticated things
Cryptography view on the Blockchain
As you are aware, every transaction in a blockchain is spread around nodes in a peer-to-peer manner so that no one can identify the transaction’s original source. In order to fully safeguard it, blockchain requires sophisticated level encryption.
Types of Cryptography
a) Symmetric
b) Asymmetric
There are fundamentally two types of cryptography
Symmetric Cryptography
- This method uses only one mutually agreed upon ‘private key’ (secret key) by the sender and the receiver, both to encrypt and to decrypt the data.
- Even though this process is faster, it is easily hackable
Asymmetric Cryptography
- This method uses a pair of Public key and private key.
- This public key is distributed amongst all the users in the network while each user has their own private key (secret key)
Algorithms in Asymmetric Cryptography
Cryptography uses a complex algorithm for secure transmission of messages over the network.
Asymmetric cryptography primarily uses two types of algorithms
- Sign-Verify
- Encrypt-Decrypt
Sign and Verify algorithms uses the concept of hashing
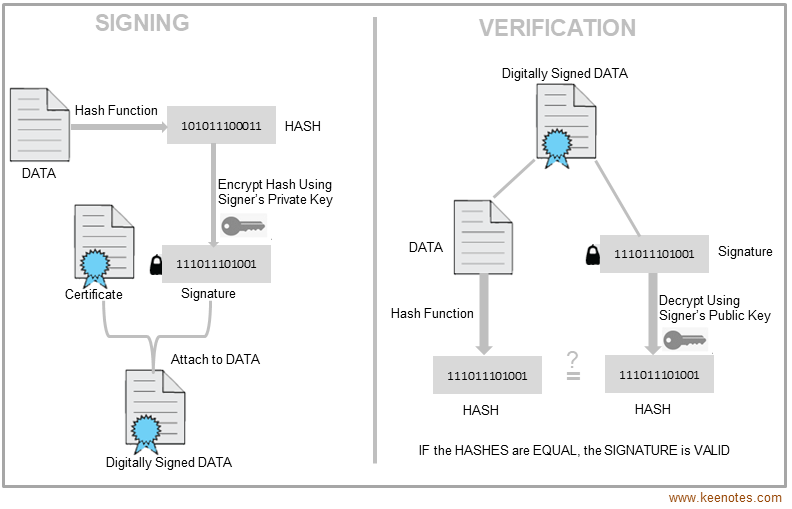
What is Hashing?
Hashing is an algorithm that encrypts data of any arbitrary length to a fixed length.
- This fixed length output is a smaller representation of the original data and is called Digest or Hashing
- Hashes can be used validate the data that came from as each digest is uniquely tied to the original message